Yes. Mugshot Investigator uses encrypted storage with role-based access and audit logs, aligned to CJIS and state privacy requirements.
Yes. Mugshot Investigator is vendor-neutral and built for interoperability with your existing workflows.
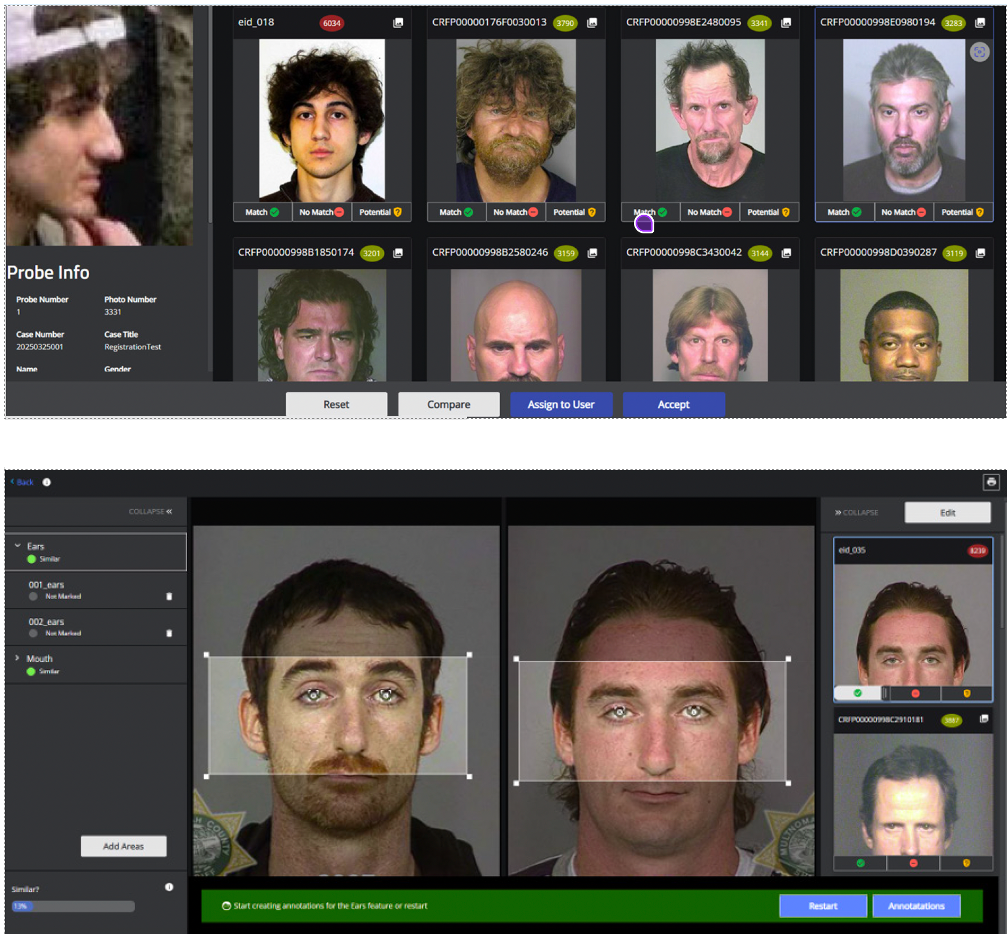
Yes. You can upgrade to Reveal - FR Investigator at any time to enable NIST-validated facial recognition and forensic-grade verification.
Automated image-quality checks, fast access to booking photos, and advanced search reduce manual work and accelerate identification.
Role-based access, full audit trails, and policy-based governance for expungement/public release provide defensible oversight end to end.
Yes. Mugshot Investigator supports cross-agency search and real-time data sharing, scaling from local agencies to statewide deployments.
Yes. Mugshot Investigator uses encrypted storage with role-based access and audit logs, aligned to CJIS and state privacy requirements.
Yes. Mugshot Investigator is vendor-neutral and built for interoperability with your existing workflows.
Yes. You can upgrade to Reveal 360 at any time to enable NIST-validated facial recognition and forensic-grade verification.
Automated image-quality checks, fast access to booking photos, and advanced search reduce manual work and accelerate identification.
Role-based access, full audit trails, and policy-based governance for expungement/public release provide defensible oversight end to end.
Yes. Mugshot Investigator supports cross-agency search and real-time data sharing, scaling from local agencies to statewide deployments.
Copyright © NEC Corporation of America 2026. All rights reserved.